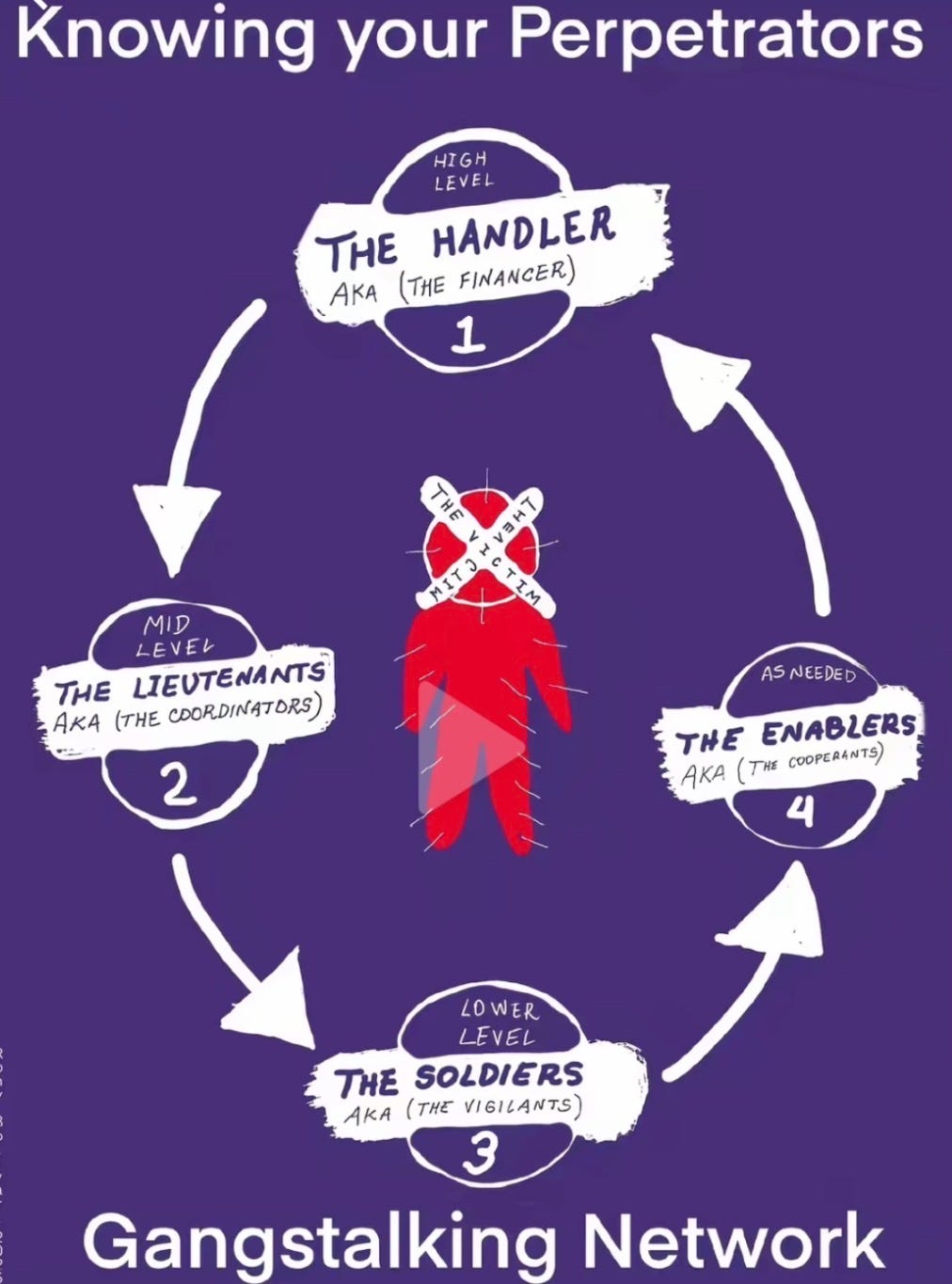
KNOWING YOUR PERPETRATORS:
The Handler aka The Financer
The handler is the central figure who initiates and directs the entire network. They are typically someone with a personal grudge, professional interest, or perceived authority over the target-such as a former acquaintance, coworker, ex-partner, or even a low-level operative from law enforcement, intelligence, or a private entity. The handler identifies the target, compiles initial intelligence (e.g., via hacking, surveillance, or social connections), and recruits or assigns the broader network. Once the operation is underway, the handler often steps back to avoid direct exposure, issuing remote instructions via encrypted apps, intermediaries, or coded signals.
• Characteristics: Often described as manipulative and obsessive, with access to resources like databases or informants. They might be "loosely known" to the target initially but become invisible as the stalking escalates. In some accounts, handlers are linked to government programs (e.g., COINTELPRO-style operations) or corporate retaliation, motivated by envy, control, or silencing dissent.
• Tactics: Scheming phase lasts 1-3 months, involving background checks, NDA signings for recruits, and staging (e.g., planting cameras in frequented stores). They ensure the operation starts covertly to erode the target's sanity before going overt.
The Lieutenants aka The Coordinators
• Role: These are portrayed as direct subordinates to the handler, managing day-to-day operations. They might include former intelligence operatives, local law enforcement, or community leaders who divide tasks among lower-level participants.
They allegedly use tools like group chats or signaling systems (e.g., color-coded clothing, hand signals, or vehicle patterns) to coordinate harassment without direct contact.
• Characteristics: Often locals familiar with the target's routines, such as neighbors or coworkers. They recruit others by spreading false rumors (e.g., labeling the target as a criminal or threat) to justify involvement.
• Formation Step: Handlers delegate to these coordinators, who expand the network by enlisting "proxies" in the target's community, workplace, or social circles.
The Enablers aka The Cooperants
Role: These include tangential participants who allegedly provide logistical support, such as hacking devices, tampering with utilities, or preading slander online to isolate the target. In extreme narratives, this extends to medical professionals or businesses complicit in sabotage
• Characteristics: Often professionals or institutions (e.g., telecom ompanies for wiretapping), portrayed as part of a larger "system."
• Formation Step: Integrated as the network scales, ensuring sustained ressure through non-physical means.

The fked up part about this is that they put so much time and energy into this and they know where we are at all times whether whether we have tech on us or not we can never escape from their grasp no matter what we do. But they can't find murderers, rapists, or bank robbers or missing children. They can't find out who's breaking in our homes. Got it!
We absolutely know who did this to us and why. Burns, deaths, and illnesses. It so sad.. so disappointed. Solace Advocates will help with physical and mental health...